.breeze
Make compliance a breeze
The setup
Devon runs npm install — or cargo add — and trusts the ecosystem.
But somewhere in those 847 transitive packages, there's a CVE from 2019 that nobody noticed. Legal wants license clarity. Security wants vulnerability reports. And Devon just wants to ship.
Sound familiar?
The gap
Your code is solid. You write tests. You review PRs. But your supply chain? That's a black box.
A CVE gets announced — are you affected?
Legal asks about licenses — what do you tell them?
A security audit looms — where do you even start?
The packages you depend on depend on packages that depend on packages. And any one of them could be the problem.
The reframe
The law shouldn't be a roadblock for your business.
The Cyber Resilience Act is coming. But here's the thing: what regulators want is what good teams already need.
Clear inventory
Know every dependency in your tree
Fast response
Spot vulnerabilities before they become incidents
Traceable decisions
Understand how each package entered your project
This isn't about checking compliance boxes. It's about shipping with confidence.
Start with visibility. The compliance story writes itself.
The solution
See what you're actually shipping.
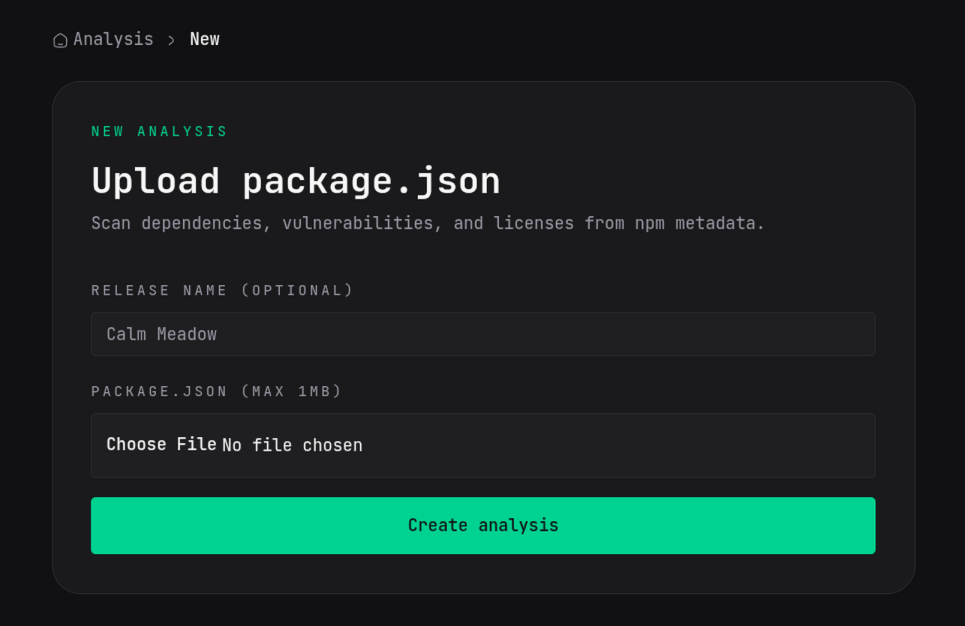
Upload your package.json or Cargo.toml. In minutes, you'll see everything.
Every dependency — direct and transitive
Not just what you installed. Everything that came along for the ride. Trace any package back to its origin in your dependency tree.
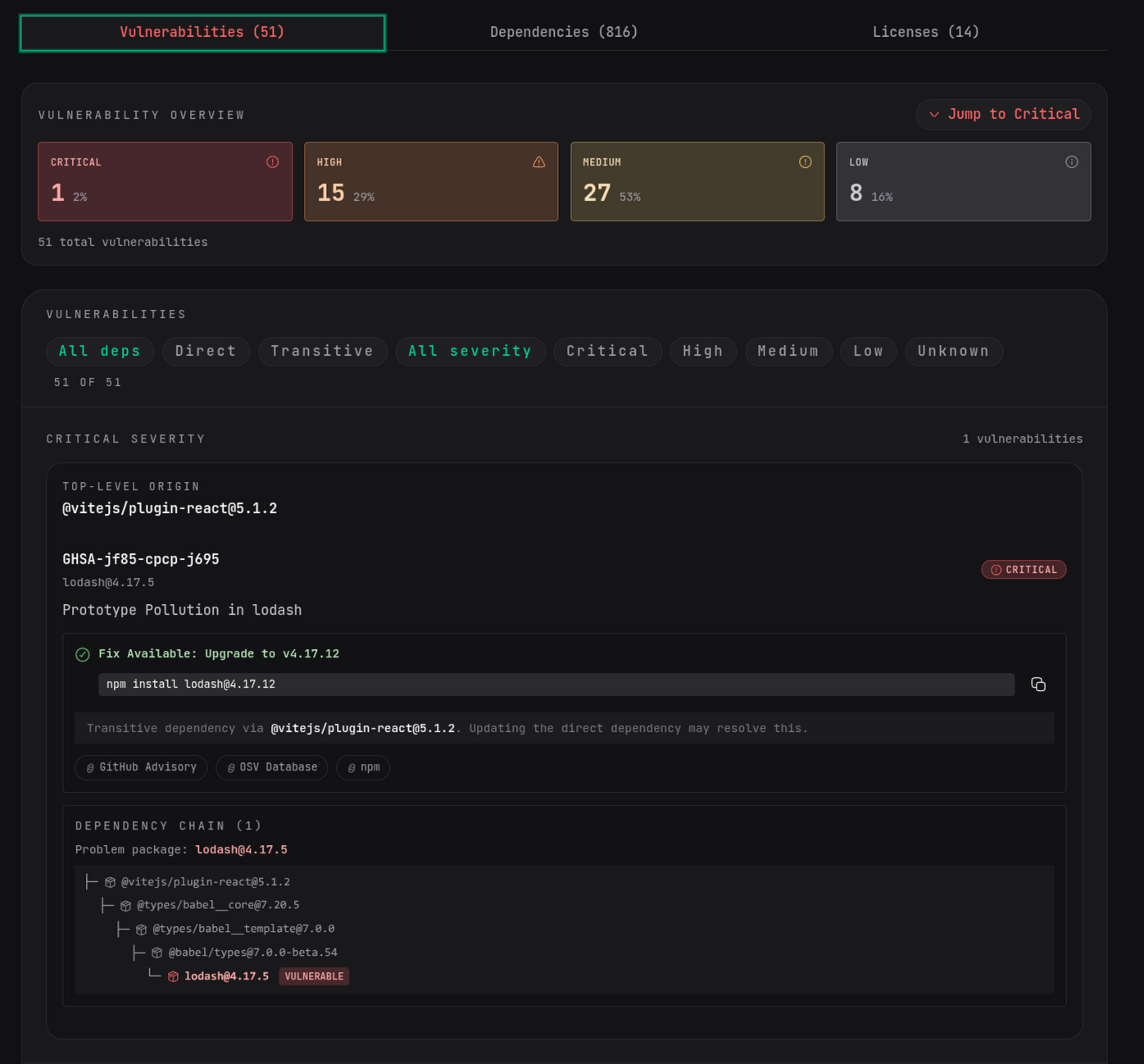
Every known vulnerability — with context
OSV-powered scanning finds CVEs across your entire supply chain. See which vulnerabilities are critical, which have fixes available, and exactly which package introduced them.
Every license — no more guessing
MIT? Apache? GPL? Know what licenses you're shipping and where they come from. No more "mostly MIT, I think."
This isn't compliance theater. It's visibility that actually helps you ship safer code.
How it works
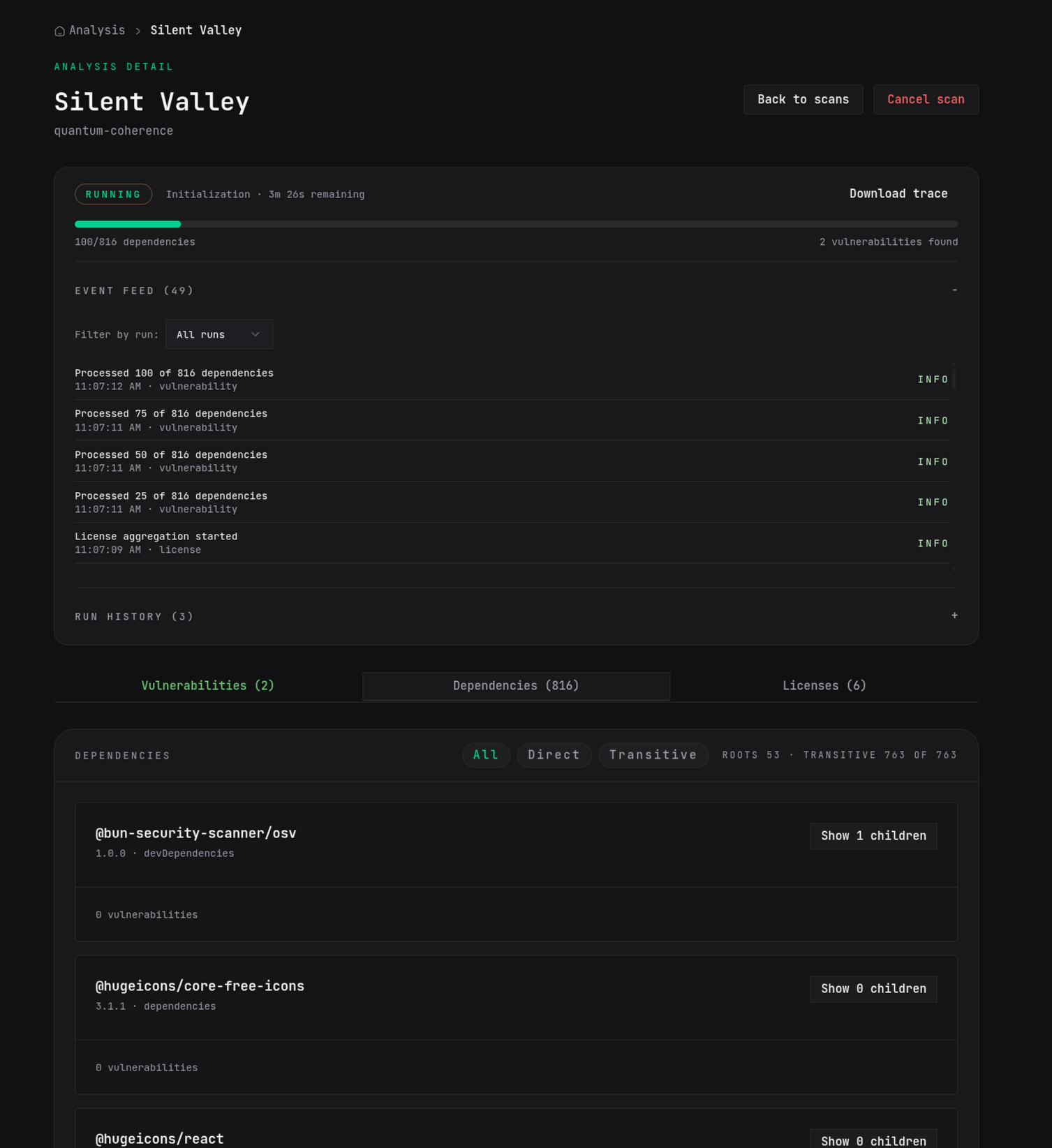
From upload to insight in minutes.
Upload
Drop your package.json or Cargo.toml. No repo integration required to get started.
Resolve
We map your entire dependency tree — direct deps, transitive deps, all of it. Up to 6 levels deep, 2000 packages.
Scan
Every package is checked against the OSV vulnerability database. We find the CVEs that actually affect your project.
Report
See vulnerabilities grouped by severity. Trace each one back through the dependency chain. Get remediation guidance.
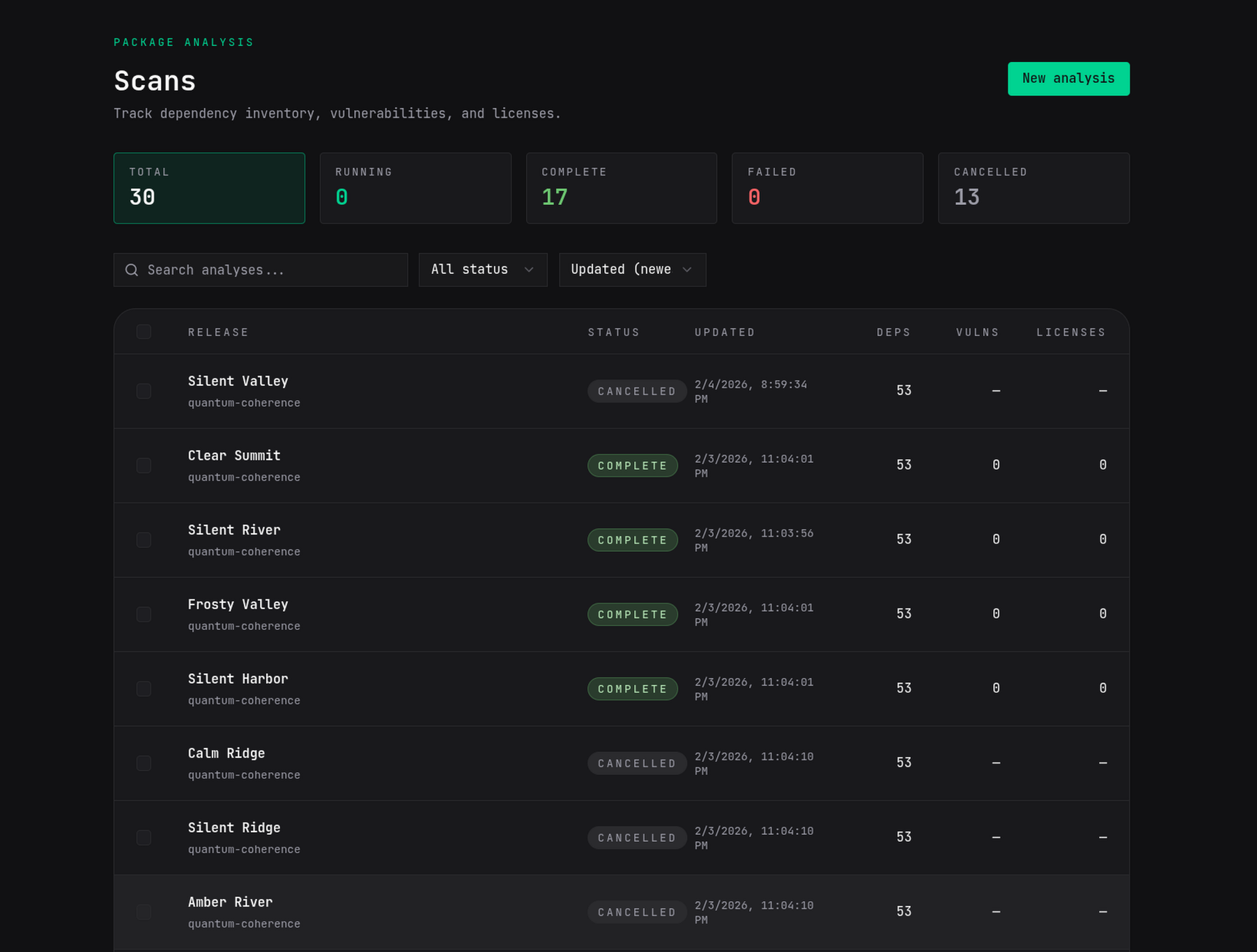
Repeat
Re-scan as your dependencies evolve. Keep your visibility current.
The bridge to the Cyber Resilience Act
Compliance is the destination. Visibility is how you get there.
The Cyber Resilience Act requires what good teams already want:
| Cyber Resilience Act Requirement | What It Really Means |
|---|---|
| SBOM lifecycle management | Know your dependencies |
| 24-hour vulnerability reporting | Spot issues fast |
| Conformity documentation | Show your work |
Today
Know your dependencies. Spot vulnerabilities. Track licenses.
Tomorrow
Conformity evidence packs.
The foundation you build now is the compliance story you'll tell later.
Who this is for
Built for teams like Devon's.
25-100 developer organizations selling software into EU markets.
You're too big for free-tier limitations. Too lean for enterprise security suites. You need compliance clarity without a dedicated team to manage it.
Set up in minutes, not months
No security specialist required
Predictable pricing that scales with your team
Devon's verdict
After 5 minutes
"Finally, I can see what's actually in my dependencies. Now when legal asks about licenses, I have an answer."
Honest about where we are
What's live vs. coming.
✓Live Now
Full dependency tree resolution
OSV vulnerability scanning
License tracking
Real-time scan progress
Run history and re-scanning
API access for automation
SBOM export (CycloneDX, SPDX)
ENISA incident reporting
CI/CD integrations
→On the Roadmap
Conformity evidence packs
We're building .breeze toward full Cyber Resilience Act compliance tooling. Today, you get the visibility foundation.
FAQ
Common questions.
Do I need to understand the Cyber Resilience Act to use .breeze?
No. .breeze gives you immediate value — dependency visibility, vulnerability scanning, license tracking — whether or not you care about compliance. Cyber Resilience Act readiness is a benefit, not a prerequisite.
What package ecosystems do you support?
We support npm (Node.js/JavaScript/TypeScript) and Cargo (Rust). More ecosystems are on the roadmap.
How fast is a scan?
Most scans complete in under 5 minutes. You'll see real-time progress as dependencies are resolved and vulnerabilities are found.
Does .breeze replace npm audit or cargo audit?
.breeze goes deeper. Built-in audit tools only check direct dependencies and miss the full picture. We resolve your full transitive tree and show you exactly how each vulnerability enters your project.
What if I find a vulnerability?
Each vulnerability shows the affected package, severity, and remediation guidance. You'll see the upgrade command (npm install or cargo add) if a fix is available, and the full dependency path so you know which top-level package to update.
Give Devon five minutes with .breeze.
Upload a package.json or Cargo.toml and see what you're really shipping.
No credit card. No repo access required. Just clarity.